- Kraken's CSO accused CertiK of extortion.
- CertiK said Kraken threatened its employees.
- Security researchers question CertiK's actions.
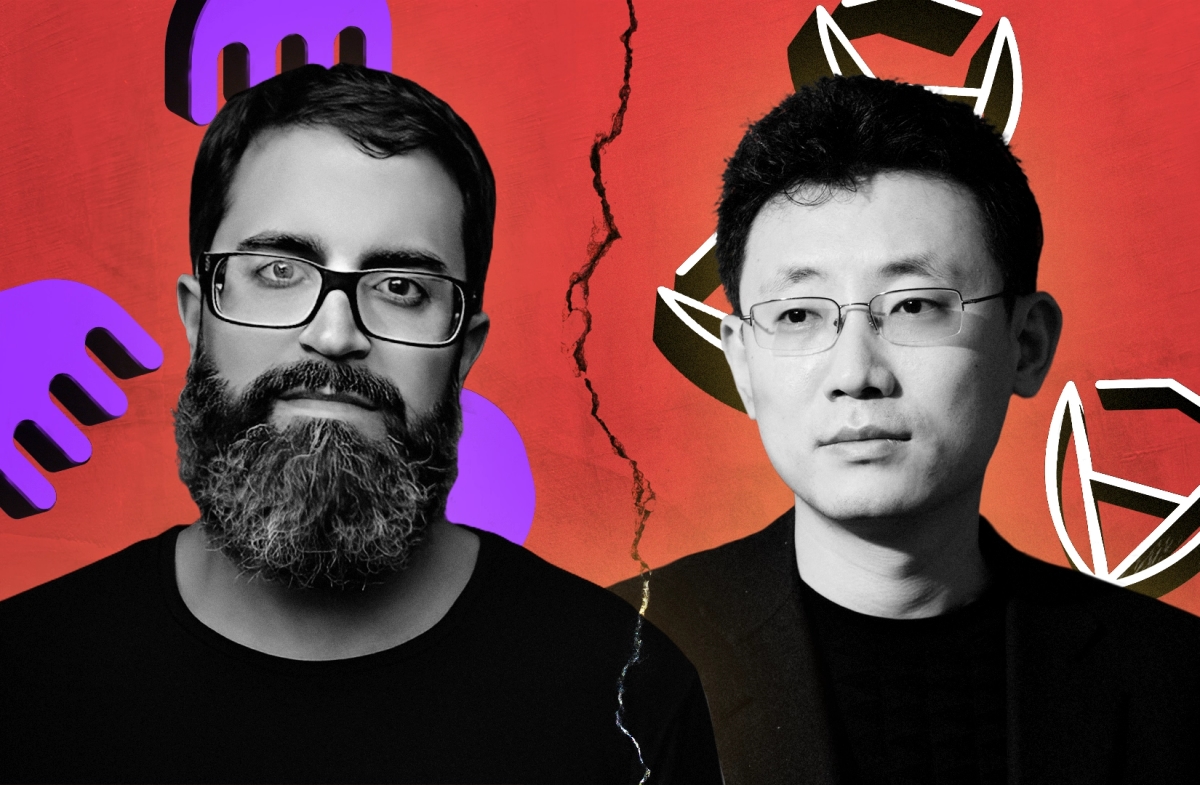
When crypto auditor CertiK announced on Wednesday that its employees had discovered and exploited a $3 million bug in American crypto exchange Kraken, eyebrows were raised.
When CertiK then said it returned the funds to the US exchange as part of a so-called white-hat operation, the firm was hit with dissent from Kraken.
“This is not white-hat hacking, it is extortion!” Nick Percoco, Kraken’s chief security officer, said in an X post on Wednesday.
Percoco said that those who found the bug said they would not return any funds until Kraken disclosed how much damage it could have caused.
CertiK didn’t take long to reply to Kraken’s statements. “They publicly accused us of theft and even directly threatened our employees, which is completely unacceptable.”

The unusual duration — and whopping $3 million size — of CertiK’s exploit sparked a flurry of questions. Usually whitehat tests of cyberdefences pick off a minimal amount of money simply to demonstrate the vulnerability.
“That’s an incredible amount to take in the interest of a whitehat exploit,” Michael Lewellen, head of solutions at competing auditing firm OpenZeppelin, told DL News.
Lewellen said that security researchers have been fired for this kind of behaviour.
“If a security researcher at any other reputable audit firm committed this sort of exploit, they’d be fired and disowned immediately,” he said.
“You never steal funds from a client unless there’s some immediate danger with no time to alert a team and even then you’re taking a big risk that many audit firms prefer not to take on for these reasons.”
‘The moment you discover something is wrong, you must reach out for the safety of users.’
— Pascal Caversaccio, security researcher
Pascal Caversaccio, an independent security researcher, said it’s strange that CertiK’s test of Kraken’s system lasted days. It should have been resolved within minutes.
“The moment you discover something is wrong, you must reach out for the safety of users,” he told DL News. “This is so stupid. Not only from a security perspective but also from a business perspective.”

There are other abnormalities.
Onchain records show that a CertiK-linked address sent funds to the DeFi protocol Tornado Cash, which was sanctioned by the US Treasury Department’s Office of Foreign Assets Control, or OFAC.
Tornado Cash angle
Though CertiK has returned assets to Kraken, sending some through Tornado Cash could violate US sanctions. According to OFAC’s website, the penalties for doing so can exceed several million dollars.
Lewellen said that using Tornado Cash for whitehat hacking is odd.
“I have never heard of a whitehat making use of Tornado Cash, especially given the sanctions risk,” he said. “You typically aren’t using Tornado Cash post-sanctions unless you’re already committing a crime and the risk of violating sanctions is outweighed.”

Other portions of the funds CertiK withdrew from Kraken were sent to ChangeNOW, a crypto exchange that doesn’t require know-your-customers checks. CertiK also swapped USDT stablecoins it withdrew from Kraken for ETH.
“If you are a whitehat, you do not do this,” Taylor Monahan, a crypto security expert, said on X.
CertiK did not immediately respond to a request for comment and has not addressed these transactions publicly.
Tim Craig is a DeFi Correspondent at DL News. Got a tip? Email him at tim@dlnews.com.